This is the post I promised I'd write when I talked about Cloud and BYOD as part of my "Do security like a start-up or get fired" series.
I created and delivered this presentation for events in Sydney, Canberra and Melbourne. The presentations received some press coverage, in particular this ZDNet article written by Michael Lee which garnered over 110 Tweets and 70+ LinkedIn shares including mentions from the likes of Cisco, IBM, SAP, Good Technology, Palo Alto Networks and of course NetIQ.
As this is a presentation masquerading as a blog post, it will be different to my usual posts. There are a bunch of images littered throughout, which are all slides from my presentation deck. As a result, you'll see some text as images because they were slides. I've kept it this way instead of typing everything out to give you a better feel for the actual presentation.
I’m going to cover 3 things:
Your barista’s doing it.
Google chairman Eric Schmidt is doing it.
It’s the viral video of 2012, holds the Guinness world record for the most likes on YouTube and has spawned more spoof videos than any other this year.
My point, other than being able to work Gangnam Style into my presentation, is that all everyone wants to talk about this year in the enterprise is BYOD. Sure, people still talk about Cloud, but in the words of the Black Eyed Peas, that’s so two thousand and late. So, the real title of my presentation is...
As most of you know, Google gives you suggestions as you type. Here’s what “bring your own” reveals.
Three out of the four suggestions are related to the same thing.
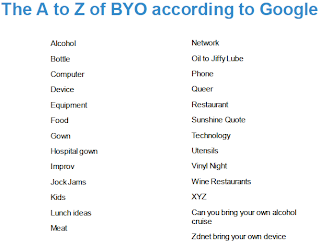
Some come up with what’s known as the A to Z of Google search terms. Here’s one for “bring your own”.
There’s a few interesting ones on the list which I won’t comment on. The point of this is that you can classify the list into 2 distinct categories.
The driver for BYOD is essentially the combination of these categories crossing over into the enterprise.
But the key message I want to make is this.
That's right. You cannot deal with BYOD by dealing with BYOD. By the end of the presentation (blog post), it should be clear why this is true.
When I ask this question, almost everyone says "no". In reality, almost everyone has. We just know it better as the five stages of grief.
In speaking with organisations about BYOD, I’ve found they tend to go through the five stages.
This is where IT says no. It’s all too difficult and presents too much of a risk to the organisation so it’s much easier just to deny everyone the privilege. They also pretend it’s not happening and hope that they will never have to deal with it once they’ve said no.
The “no” answer, usually falls on deaf ears. IT gets asked again and they keep saying “no”, until they get the question from people at the executive level. In fact, this is commonly the compelling reason that forces IT to relax their stance and find a way to get it done. I’ve actually sat in a meeting before with one of the large Australian banks and had the head of security step out of the meeting to take a call about the CEO wanting to get access to corporate email via their iPad. Of course, it got done despite the fact that it broke policy.
Once you make single exception, there are always other exceptions. Eventually, it becomes too difficult to manage and IT has to relent, but only to a certain extent. Usually, IT lets you have limited access and this starts with email. The interesting thing is that there is a perception that email is one of the least sensitive applications and hence presents minimal risk to the organisation. This is why it’s usually one of the first systems that are moved to the Cloud. The reality is that corporate email is one of the most sensitive applications any organisation has. The fact is however, this is usually what happens.
This is where IT realises that even though they thought they addressed the issue by compromising, an increasing number of people continue to go around them. Users are a smart bunch at getting around IT departments and IT security policy, especially when we have full control of the device we’re using. At this point, IT has 2 options:
Every organisation will get to this point whether they like it or not. It’s just a matter of time. To remain secure and evolve with the times, you have to. It’s better to go in with eyes wide open than to dig your heels in and pretend it’s not happening.
The reality today is that most organisations are somewhere between bargaining and acceptance, skewed towards the bargaining stage. The point to take away here is that when it comes to the freight train that is BYOD...
You can’t have a track that ends.
It has to look more like this.
Where you have well defined paths, but allow flexibility to choose the one that is appropriate for the situation and destination.
You can’t put a wall up or make it the end of the line otherwise people, usually the ones with the authority to make you change your stance, find ways around you. They will eventually replace you with someone who can be that creative "yes" person the modern enterprise needs.
You may have noticed that I've been using the BYOD term a lot. But as I said up front, when you actually have to deal with it, you will quickly realise it’s actually about more than dealing with devices. To deal with BYOD, you have to handle a raft of other issues. BYOD is essentially about handling employees using what they choose for business purposes, not just a device of choice. It is about the Consumerisation of IT and its intersection with Enterprise IT.
Since we’re talking about transport, let me talk about airports.
Everyone generally knows how airports function, but we never take the time to think about it. We typically meander through because we want to get to our destination with as little fuss as possible. Airports are businesses and perform an essential function, but need to be self-sustainable from a financial standpoint. They provide infrastructure services to support the experiences we have in an airport; fuel for the planes, spaces for shops, airline lounges and so on. But when you strip everything back, there are two essential things about an airport that we cannot do without.
The first is ensuring that passengers are able to get to their destination safely. As travellers, we want safety. Without safety, we would not fly anywhere. That’s why we put up with the painful security checks at every airport.
The second is ensuring that the airport experience is as pleasant as possible, even though it may not seem that way. As consumers, we are demanding and expect more than just “pleasant”. Anything less than good and we complain that the airport is not up to standard. We want to be impressed, even if we won't admit to it. For example, Kuala Lumpur international airport has a jungle walk inside the terminal.
Back to safety; to minimise risk and ensure an acceptable level, airports and the relevant services within the terminal make us jump through all sorts of hoops to gain access to things. Airports control access to designated areas and services based on forms of identification combined with monitoring activity and observed behaviour. The only reason this works is because of identity.
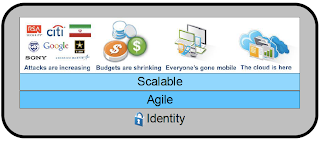
But not just any identity. The key is that real-world identities are scalable.
If you’ve seen (or read) my Identity in an agile world presentation, you’ll remember that the reason real world identities are scalable is because: for access to things, it doesn’t matter who I am; it matters what I am.
This is why the fact that my boarding pass...
Gets me onto a plane...
Has nothing to do with me being Ian Yip. It's because the boarding pass is an acceptable credential to gain access to the plane as a passenger. It just needs to be genuine and have the correct date and flight number on it. Even when it is cross-checked with a passport on international flights prior to boarding, the name on the boarding pass is irrelevant. The staff at the gate are simply checking that they match, which raises the level of assurance of the credential (boarding pass) I'm using.
When we fly, we have a choice. Imagine if the only choice we had when we fly was this plane.
And this is where you sit.
Would you want to use it? What would you think if that was your only option? Would you pay more to fly this in this other plane?
And your seats looked like this?
Right about now, you're probably thinking...
In the context of the topic at hand, various aspects our experiences in airports are relevant. If you think about the airport as being the organisation, the rest of the things on this list map logically.
The key point being that we have a choice of airlines, just like we have a choice of devices if corporate policies allow. Airports manage to remain secure despite the choices they present us. Sure there are inconveniences we have to deal with but we pay the price for the benefits.
Now, let’s consider this point. Would we lock the planes down but let everyone wander around freely? This only works at airshows, not in a real airport. We would never use an airport if this was the case. So why do so many organisations attempt to deal with BYOD using only Mobile Device Management (MDM) technologies? Doing so is effectively locking the plane down but leaving everything else open. MDM is a tactical feature, not an organisational strategy.
To deal with BYOD and subsequently the consumerisation of IT, you need all the other things that make an airport secure while balancing it with the flexibility of experiences a good airport provides. In other words...
Remember the jungle within Kuala Lumpur’s terminal?
Airports add services like this to make the experience better. It balances out all the inconveniences we have to endure in making our way through airports. Psychologically, this is similar to why employees are starting make their own choices when using applications to do their jobs.
How many of us have tried to use an enterprise application (e.g. ERP or CRM) and complained about how bad it was? They end up not getting used and we revert to something basic like spreadsheets, which aren't all that nice to use anyway. We’ve been behaving this way for quite some time and have been forced to get used to it due to the lack of available options. The difference today is that the innovation in the mobile space has extended to applications and we’re able to use great, consumer-grade applications for business needs (which aren't necessarily sanctioned by corporate IT). This is the driver behind users bringing their own applications, or if we follow the BYO meme, the Bring Your Own Application (BYOA) trend that is upon us.
Consumerisation is now extending to our social logins. The following options are arguably the dominant identities we use online: Facebook, Twitter, Google, LinkedIn.
Given the lines between personal and business are starting to blur, it is inevitable that our social identities start to extend into the enterprise. While we may not be at the stage where they can be used as being highly trusted identifiers for critical systems, they do provide a way for enterprises to use a lightweight identifier for their employees and customers.
In fact, a lot of organisations are looking at using social logins for their customers. Retailers are the most common type of organisation here, although the UK government announced recently that they were looking at allowing this for citizens. Washington State in the US allows voters to register through Facebook. We haven’t gotten to the stage where most organisations are actively trying to implement the same thing for their employees, but given that many will have the foundational components in place for their customers, it’s not a stretch to extend it to employees and provide a lightweight identifier internally for less critical systems without forcing employees to sign in. For example, my iPad is signed in to Twitter by default at the operating system layer. With the latest release of iOS, Apple added Facebook to sit side-by-side with our Twitter identity. In other words, it's relatively easy to Bring Your Own Identity (BYOI) to your day job, especially when you BYOD.
What about Cloud? Could employees conceivably bring their own Cloud?
Guess what? It’s already happening with business units procuring their own SaaS applications without the knowledge of IT. This has been caused by IT security saying no all the time and instead of trying to negotiate, they simple use a credit card and pay for a service with the approval of the business head. This is more common than most of us realise.
I said “pay”, but this typically starts off free. I’ll give you a simple example. Have you used Google Apps or Dropbox to store documents so you can easily collaborate with colleagues? It’s for business use and it’s free! Guess what? You’re bringing your own cloud in the form of SaaS. Again, instead of saying “no”, IT security departments are better off saying “yes” and working with the business users to mitigate the risks this poses.
Could we go further? What about the more technically minded that aren’t necessarily part of IT spinning up a new server instance within a Cloud service provider and building their own applications on top of this without the involvement of IT? This will be less common than bringing your own Cloud in the form of SaaS, but this vector actually poses more of a security risk than SaaS because someone who is technical enough to do so isn’t necessarily trained in IT security. In fact, the unfortunate situation we have today is that many technical people and developers aren’t sufficiently trained in IT security. This is something that urgently needs to be fixed. Also, the further down the infrastructure stack you go, the harder it is to secure and that's exactly what happens when someone spins up new IT infrastructure in the Cloud.
Apart from BYOD, I’ve mentioned a few other BYO acronyms.
This is by no means the final list. It’s still early days and the list will evolve. Organisations need to be agile enough to deal with trends and issues as they arise. As many of us found with Cloud and BYOD, these things creep up a lot more quickly than we expect and if you aren’t prepared, it makes things difficult, especially when it comes to security.
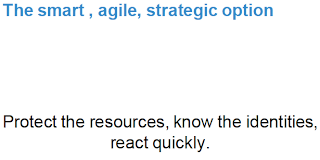
You can generalise the various approaches to dealing with BYO* into the following list, three of which are tactical and one of which is strategic.
By tactical, I mean that you can address one aspect of security, but you will find holes in other areas. It’s better to adopt the strategic approach so that you can react more quickly and focus on what it is you’re trying to do. Strategic approaches allow you to address a larger "risk and threat surface area" with less long-term spend.
In focusing, you should be thinking about what you are actually trying to protect. In reality, it’s the information.
Notice how I’ve said information and not just data. There’s a subtle distinction best illustrated by a joke about all the PINs in the world being exposed. It was simply a list of all the numbers from 0000 to 9999. That list is simply data. Add things like account numbers to the PIN and you have information. The difference between information and data is context.
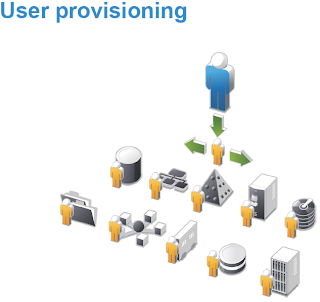
What this means is that the strategic approach to cover your bases in the long term and become agile, is to focus on protecting the information. You do that by controlling access to the information, knowing about the identities accessing the information, what is being done to the information, when things are being done and subsequently being able to react quickly when appropriate.
I’ve already mentioned a few challenges. Here’s a list of some important ones that need to be addressed if you want to deal with the consumerisation of IT within the enterprise effectively.
Many of them have to do with human behaviour, which cannot be fixed by technology alone. It’s about altering culture. It’s about rethinking security.
There are two on this list that I want to focus on for a few moments:
That said, there are benefits to be had. I’ve already mentioned a few, but here is a list of the top 5 benefits many organisations cite.
Notice I don’t have something commonly cited in the list of benefits and that is in the reduction of hardware costs. It seems logical that in not having to buy employees new equipment, you save money. But these costs will manifest themselves in other ways, the most obvious being the expenditure required in dealing with BYO.
Here’s a list of things that will help secure the Gangnam Style of the enterprise.
It’s not an exhaustive list, nor are they all appropriate for every organisation, but it’s a good starting point. To expand on each in the list:
In summary, if you don’t remember anything else, please at least keep the following 5 things front of mind.
I created and delivered this presentation for events in Sydney, Canberra and Melbourne. The presentations received some press coverage, in particular this ZDNet article written by Michael Lee which garnered over 110 Tweets and 70+ LinkedIn shares including mentions from the likes of Cisco, IBM, SAP, Good Technology, Palo Alto Networks and of course NetIQ.
As this is a presentation masquerading as a blog post, it will be different to my usual posts. There are a bunch of images littered throughout, which are all slides from my presentation deck. As a result, you'll see some text as images because they were slides. I've kept it this way instead of typing everything out to give you a better feel for the actual presentation.
IT security implications of BYO* for enterprises
The BYO in the title stands for “bring your own”. The term dominating the headlines is Bring Your Own Device (BYOD) but it's about so much more than just the 'D' in BYOD. The use of the “*” is a reference to the fact it’s not just about employees bringing their own devices into the work place; it's about a trend towards employees bringing their own technology into the workplace.I’m going to cover 3 things:
- Why BYO is top of mind.
- Understanding BYO.
- How to secure BYO.
Your barista’s doing it.
Google chairman Eric Schmidt is doing it.
It’s the viral video of 2012, holds the Guinness world record for the most likes on YouTube and has spawned more spoof videos than any other this year.
My point, other than being able to work Gangnam Style into my presentation, is that all everyone wants to talk about this year in the enterprise is BYOD. Sure, people still talk about Cloud, but in the words of the Black Eyed Peas, that’s so two thousand and late. So, the real title of my presentation is...
How to secure the Gangnam Style of Enterprise IT
While we’re on Google, I thought I’d see what their algorithms thought about the BYO meme since we rely so much on search today. It’s a convenient, mildly scientific way to get at what’s top of mind in terms of things we want to know about or find solutions for.As most of you know, Google gives you suggestions as you type. Here’s what “bring your own” reveals.
Three out of the four suggestions are related to the same thing.
Some come up with what’s known as the A to Z of Google search terms. Here’s one for “bring your own”.
There’s a few interesting ones on the list which I won’t comment on. The point of this is that you can classify the list into 2 distinct categories.
The driver for BYOD is essentially the combination of these categories crossing over into the enterprise.
But the key message I want to make is this.
That's right. You cannot deal with BYOD by dealing with BYOD. By the end of the presentation (blog post), it should be clear why this is true.
When I ask this question, almost everyone says "no". In reality, almost everyone has. We just know it better as the five stages of grief.
In speaking with organisations about BYOD, I’ve found they tend to go through the five stages.
The “no” answer, usually falls on deaf ears. IT gets asked again and they keep saying “no”, until they get the question from people at the executive level. In fact, this is commonly the compelling reason that forces IT to relax their stance and find a way to get it done. I’ve actually sat in a meeting before with one of the large Australian banks and had the head of security step out of the meeting to take a call about the CEO wanting to get access to corporate email via their iPad. Of course, it got done despite the fact that it broke policy.
Once you make single exception, there are always other exceptions. Eventually, it becomes too difficult to manage and IT has to relent, but only to a certain extent. Usually, IT lets you have limited access and this starts with email. The interesting thing is that there is a perception that email is one of the least sensitive applications and hence presents minimal risk to the organisation. This is why it’s usually one of the first systems that are moved to the Cloud. The reality is that corporate email is one of the most sensitive applications any organisation has. The fact is however, this is usually what happens.
This is where IT realises that even though they thought they addressed the issue by compromising, an increasing number of people continue to go around them. Users are a smart bunch at getting around IT departments and IT security policy, especially when we have full control of the device we’re using. At this point, IT has 2 options:
- Stick their head in the sand, pretend it’s not happening and attempt to lock everything down thus getting in the way of business.
- Deal with the situation at hand in a constructive, business-centric manner. We forget all too often that IT is a business enabler. IT security, should also be a business enabler.
Every organisation will get to this point whether they like it or not. It’s just a matter of time. To remain secure and evolve with the times, you have to. It’s better to go in with eyes wide open than to dig your heels in and pretend it’s not happening.
The reality today is that most organisations are somewhere between bargaining and acceptance, skewed towards the bargaining stage. The point to take away here is that when it comes to the freight train that is BYOD...
 |
| Photo credit: Steve Wilson |
You can’t have a track that ends.
 |
| Photo credit: Cassandra Jowett |
It has to look more like this.
 |
| Photo credit: Les Chatfield |
Where you have well defined paths, but allow flexibility to choose the one that is appropriate for the situation and destination.
You can’t put a wall up or make it the end of the line otherwise people, usually the ones with the authority to make you change your stance, find ways around you. They will eventually replace you with someone who can be that creative "yes" person the modern enterprise needs.
You may have noticed that I've been using the BYOD term a lot. But as I said up front, when you actually have to deal with it, you will quickly realise it’s actually about more than dealing with devices. To deal with BYOD, you have to handle a raft of other issues. BYOD is essentially about handling employees using what they choose for business purposes, not just a device of choice. It is about the Consumerisation of IT and its intersection with Enterprise IT.
Since we’re talking about transport, let me talk about airports.
 |
| Photo credit: Oliver Mallich |
Everyone generally knows how airports function, but we never take the time to think about it. We typically meander through because we want to get to our destination with as little fuss as possible. Airports are businesses and perform an essential function, but need to be self-sustainable from a financial standpoint. They provide infrastructure services to support the experiences we have in an airport; fuel for the planes, spaces for shops, airline lounges and so on. But when you strip everything back, there are two essential things about an airport that we cannot do without.
The first is ensuring that passengers are able to get to their destination safely. As travellers, we want safety. Without safety, we would not fly anywhere. That’s why we put up with the painful security checks at every airport.
 |
| Photo credit: Inha Leex Hale |
The second is ensuring that the airport experience is as pleasant as possible, even though it may not seem that way. As consumers, we are demanding and expect more than just “pleasant”. Anything less than good and we complain that the airport is not up to standard. We want to be impressed, even if we won't admit to it. For example, Kuala Lumpur international airport has a jungle walk inside the terminal.
Back to safety; to minimise risk and ensure an acceptable level, airports and the relevant services within the terminal make us jump through all sorts of hoops to gain access to things. Airports control access to designated areas and services based on forms of identification combined with monitoring activity and observed behaviour. The only reason this works is because of identity.
But not just any identity. The key is that real-world identities are scalable.
 |
| Photo credit: Stefano Chiarelli |
If you’ve seen (or read) my Identity in an agile world presentation, you’ll remember that the reason real world identities are scalable is because: for access to things, it doesn’t matter who I am; it matters what I am.
This is why the fact that my boarding pass...
Gets me onto a plane...
 |
| Photo credit: Jay-Oh |
Has nothing to do with me being Ian Yip. It's because the boarding pass is an acceptable credential to gain access to the plane as a passenger. It just needs to be genuine and have the correct date and flight number on it. Even when it is cross-checked with a passport on international flights prior to boarding, the name on the boarding pass is irrelevant. The staff at the gate are simply checking that they match, which raises the level of assurance of the credential (boarding pass) I'm using.
When we fly, we have a choice. Imagine if the only choice we had when we fly was this plane.
 |
| Photo credit: Tim Bunce |
And this is where you sit.
 |
| Photo credit: Bill Abbott |
Would you want to use it? What would you think if that was your only option? Would you pay more to fly this in this other plane?
 |
| Photo credit: Vox Efx |
And your seats looked like this?
 |
| Photo credit: Andy Mitchell |
Right about now, you're probably thinking...
In the context of the topic at hand, various aspects our experiences in airports are relevant. If you think about the airport as being the organisation, the rest of the things on this list map logically.
The key point being that we have a choice of airlines, just like we have a choice of devices if corporate policies allow. Airports manage to remain secure despite the choices they present us. Sure there are inconveniences we have to deal with but we pay the price for the benefits.
Now, let’s consider this point. Would we lock the planes down but let everyone wander around freely? This only works at airshows, not in a real airport. We would never use an airport if this was the case. So why do so many organisations attempt to deal with BYOD using only Mobile Device Management (MDM) technologies? Doing so is effectively locking the plane down but leaving everything else open. MDM is a tactical feature, not an organisational strategy.
To deal with BYOD and subsequently the consumerisation of IT, you need all the other things that make an airport secure while balancing it with the flexibility of experiences a good airport provides. In other words...
Remember the jungle within Kuala Lumpur’s terminal?
Airports add services like this to make the experience better. It balances out all the inconveniences we have to endure in making our way through airports. Psychologically, this is similar to why employees are starting make their own choices when using applications to do their jobs.
How many of us have tried to use an enterprise application (e.g. ERP or CRM) and complained about how bad it was? They end up not getting used and we revert to something basic like spreadsheets, which aren't all that nice to use anyway. We’ve been behaving this way for quite some time and have been forced to get used to it due to the lack of available options. The difference today is that the innovation in the mobile space has extended to applications and we’re able to use great, consumer-grade applications for business needs (which aren't necessarily sanctioned by corporate IT). This is the driver behind users bringing their own applications, or if we follow the BYO meme, the Bring Your Own Application (BYOA) trend that is upon us.
Consumerisation is now extending to our social logins. The following options are arguably the dominant identities we use online: Facebook, Twitter, Google, LinkedIn.
Given the lines between personal and business are starting to blur, it is inevitable that our social identities start to extend into the enterprise. While we may not be at the stage where they can be used as being highly trusted identifiers for critical systems, they do provide a way for enterprises to use a lightweight identifier for their employees and customers.
In fact, a lot of organisations are looking at using social logins for their customers. Retailers are the most common type of organisation here, although the UK government announced recently that they were looking at allowing this for citizens. Washington State in the US allows voters to register through Facebook. We haven’t gotten to the stage where most organisations are actively trying to implement the same thing for their employees, but given that many will have the foundational components in place for their customers, it’s not a stretch to extend it to employees and provide a lightweight identifier internally for less critical systems without forcing employees to sign in. For example, my iPad is signed in to Twitter by default at the operating system layer. With the latest release of iOS, Apple added Facebook to sit side-by-side with our Twitter identity. In other words, it's relatively easy to Bring Your Own Identity (BYOI) to your day job, especially when you BYOD.
What about Cloud? Could employees conceivably bring their own Cloud?
Guess what? It’s already happening with business units procuring their own SaaS applications without the knowledge of IT. This has been caused by IT security saying no all the time and instead of trying to negotiate, they simple use a credit card and pay for a service with the approval of the business head. This is more common than most of us realise.
I said “pay”, but this typically starts off free. I’ll give you a simple example. Have you used Google Apps or Dropbox to store documents so you can easily collaborate with colleagues? It’s for business use and it’s free! Guess what? You’re bringing your own cloud in the form of SaaS. Again, instead of saying “no”, IT security departments are better off saying “yes” and working with the business users to mitigate the risks this poses.
Could we go further? What about the more technically minded that aren’t necessarily part of IT spinning up a new server instance within a Cloud service provider and building their own applications on top of this without the involvement of IT? This will be less common than bringing your own Cloud in the form of SaaS, but this vector actually poses more of a security risk than SaaS because someone who is technical enough to do so isn’t necessarily trained in IT security. In fact, the unfortunate situation we have today is that many technical people and developers aren’t sufficiently trained in IT security. This is something that urgently needs to be fixed. Also, the further down the infrastructure stack you go, the harder it is to secure and that's exactly what happens when someone spins up new IT infrastructure in the Cloud.
Apart from BYOD, I’ve mentioned a few other BYO acronyms.
This is by no means the final list. It’s still early days and the list will evolve. Organisations need to be agile enough to deal with trends and issues as they arise. As many of us found with Cloud and BYOD, these things creep up a lot more quickly than we expect and if you aren’t prepared, it makes things difficult, especially when it comes to security.
You can generalise the various approaches to dealing with BYO* into the following list, three of which are tactical and one of which is strategic.
By tactical, I mean that you can address one aspect of security, but you will find holes in other areas. It’s better to adopt the strategic approach so that you can react more quickly and focus on what it is you’re trying to do. Strategic approaches allow you to address a larger "risk and threat surface area" with less long-term spend.
In focusing, you should be thinking about what you are actually trying to protect. In reality, it’s the information.
Notice how I’ve said information and not just data. There’s a subtle distinction best illustrated by a joke about all the PINs in the world being exposed. It was simply a list of all the numbers from 0000 to 9999. That list is simply data. Add things like account numbers to the PIN and you have information. The difference between information and data is context.
What this means is that the strategic approach to cover your bases in the long term and become agile, is to focus on protecting the information. You do that by controlling access to the information, knowing about the identities accessing the information, what is being done to the information, when things are being done and subsequently being able to react quickly when appropriate.
I’ve already mentioned a few challenges. Here’s a list of some important ones that need to be addressed if you want to deal with the consumerisation of IT within the enterprise effectively.
Many of them have to do with human behaviour, which cannot be fixed by technology alone. It’s about altering culture. It’s about rethinking security.
There are two on this list that I want to focus on for a few moments:
- The first is skills. As your IT environment evolves, so do the skills required. One of the biggest challenges enterprises face is that many of people with the skills required are shying away from working in the enterprise due to the perceived lack of innovation. They prefer to work for small companies. The challenge for enterprises is to change that perception and you do that by changing the culture and the way you do IT.
- The second is the tricky issue of privacy. Given that devices hold a lot of personal data, it becomes paramount that organisations do not store employee personal data in the enterprise. In fact, one of the reasons many MDM deployments fail is due to the privacy concerns of employees and the concern that their employers are monitoring them during non-business hours. On the other hand, many organisations don’t want anything to do with employee personal information due to potential legal ramifications they may be subject to. Inevitably, for things to work, there needs to be compromise, but not at the expense of the requirement to NOT use more personal information in a business context than required or allowed (by the employee and regulatory requirements).
That said, there are benefits to be had. I’ve already mentioned a few, but here is a list of the top 5 benefits many organisations cite.
Notice I don’t have something commonly cited in the list of benefits and that is in the reduction of hardware costs. It seems logical that in not having to buy employees new equipment, you save money. But these costs will manifest themselves in other ways, the most obvious being the expenditure required in dealing with BYO.
Here’s a list of things that will help secure the Gangnam Style of the enterprise.
It’s not an exhaustive list, nor are they all appropriate for every organisation, but it’s a good starting point. To expand on each in the list:
- Evolve from no people to creative yes people - I’ve alluded to this a few times. Stop saying no. Say yes and be creative about mitigating the risks or people will go around you. Also, your boss will fire you and hire someone who can say yes while managing risk.
- Have an acceptable use policy for devices that is easy to understand - The first step down the BYO journey tends to be the drafting of a policy. But it is essential that it’s easy to understand. How many times have we blindly agreed to a policy because it’s too difficult to understand?
- Enforce access control policies - These should rely on identity, context and policy to protect resources. Do not allow a device to access resources if systems cannot determine the user’s identity, if it does not meet compliance standards or if it does not have prerequisite software installed. Apply context by restricting access based on factors such as location and whether the connection is encrypted.
- Automate the remediation process - Make it as simple as possible for the user to ensure device compliance by automating a majority of the remediation process. Do not rely on the user to know that they need to download and install a list of software components.
- Monitor events and activities - Monitor all devices accessing resources on the corporate network using a Security Information and Event Management (SIEM) solution that can provide auditable, actionable intelligence and can be tied to identities. In an environment filled with partially trusted, potentially compromised devices, visibility is paramount and incident response time critical.
- Use scalable identities - Reduce operational overhead in environments with many identity sources in a secure, standards-based manner by federating user identities across segmented zones and rely on trust-levels to enforce access controls. As an example, consider the overlap between internal employee identities and their online identities that I alluded to earlier when talking about BYOI. Users with their own devices are usually already logged in to their online accounts. For ease of use and transparent single sign-on, security policies can be implemented to support levels of assurance (LOA). If an employee is already signed into Twitter, internal applications can utilise that identity, but at a lower level of trust. So, an employee can potentially use their Twitter credentials to access non-sensitive parts of the intranet. But if they want to access corporate email, they are required to provide their employee credentials thus enforcing a higher LOA (thus "stepping-up" their authentication level) and asserting with greater confidence (and reduced risk) that the employee is who they claim to be.
- Provide secure devices - An alternative to allowing employees to buy and bring their own devices is to let them pick what they want and pay for it with the trade-off being that they have to allow the organisation to load required software and implement relevant controls based on IT security policies. This presents a win-win situation for both organisation and employee. They use a device of their choice without having to pay for it and can access the corporate environment in a secure and compliant manner.
- Encrypt sensitive information - Encrypt any information placed on a non-standard device that is deemed to be company property. This may include the employee’s corporate email.
In summary, if you don’t remember anything else, please at least keep the following 5 things front of mind.